As a consultancy, we’re constantly having to share and receive files with potential and actual customers. And as regular people, we also want to easily share files with family, friends, and financial advisors. But we couldn’t find a sharing tool that worked for all of our requirements, so inspired by an open-source project, we built it ourselves. And we hope you might want to use it too.
Requirements
As consultants who’ve collectively worked at a wide range of previous places, we’ve all had to use PGP email, or S/MIME, or other applications that typically require one or both users to install an application, appliance or email plugin, or to sign up to a service. We wanted a file sharing application that means:
- Users don’t have to use GPG,
- and don’t have to password-protect email attachments,
- and don’t have to set up guest SharePoint accounts and share folders,
- and don’t have to use websites they’re not sure about, or that are covered in adverts,
- and really don’t have to use GPG.
It turns out there are way more file sharing applications than we first thought, and we’ve looked at a lot of them, but each seems to have a crucial drawback. For example:
- Not being easy to use, for both the sender and the receiver.
- Requiring both parties to sign in. This is burdensome for a customer who just wants to see a quote or report, for example.
- Not offering End-to-End Encrypted (E2EE), which means the provider can see what you’re sharing. We favour a privacy-first approach.
- Being complex to set up, especially for non-technical people, or requiring hardware or software installation.
- Was completely anonymous, which makes it harder to trust received files.
So we set out to build something that met these requirements, without any of the drawbacks.
Firefox Send
Our inspiration was the relatively short-lived Firefox Send, an easy to use application that offered anonymous, End-to-End Encrypted (E2EE) file sharing. However, that anonymity became a problem as malicious users started to use it for nefarious purposes:
Firefox Send was a promising tool for encrypted file sharing. Send garnered good reach, a loyal audience, and real signs of value throughout its life. Unfortunately, some abusive users were beginning to use Send to ship malware and conduct spear phishing attacks. This summer we took Firefox Send offline to address this challenge.
Update on Firefox Send and Firefox Notes, Mozilla, September 2020
In the end, we almost totally rewrote Firefox Send; all that remains are three source files, which as per their original license we have made available here.
Trebuchet
Given the extensive rewrite it was only fair that we renamed it, and we chose Trebuchet (more on that later). We’ve worked on it for a few months, using and testing it internally. We also added more features, some of which are crucial for improved security and additional functionality:
User Sign-In
A prime example is requiring at least one person in a file share to be signed in, so that when receiving a file from a user you know it came from that user’s account:
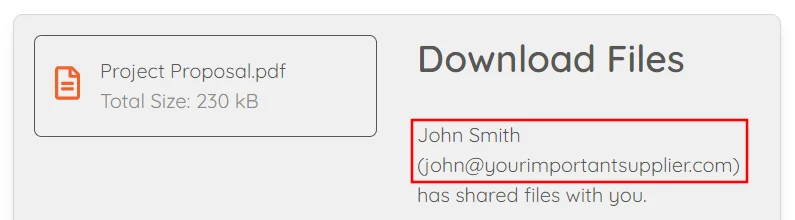
This in some way mitigates the issue that Firefox Send had, in that tools that can be used anonymously are more open to abuse.
Of course, you still need to trust that that signed-in user has shared what you expected them to, but at least you know it’s come from their account. As shared files are end-to-end encrypted, we can’t inspect them on the server. So we can’t, for example, filter out executable files or potentially malicious content. The only possible approach would be to add some filtering in the web application, which as it’s client-side (their browser) could be bypassed by a capable attacker. Regardless, that might come soon, as some protection is better than none at all.
Share Requests
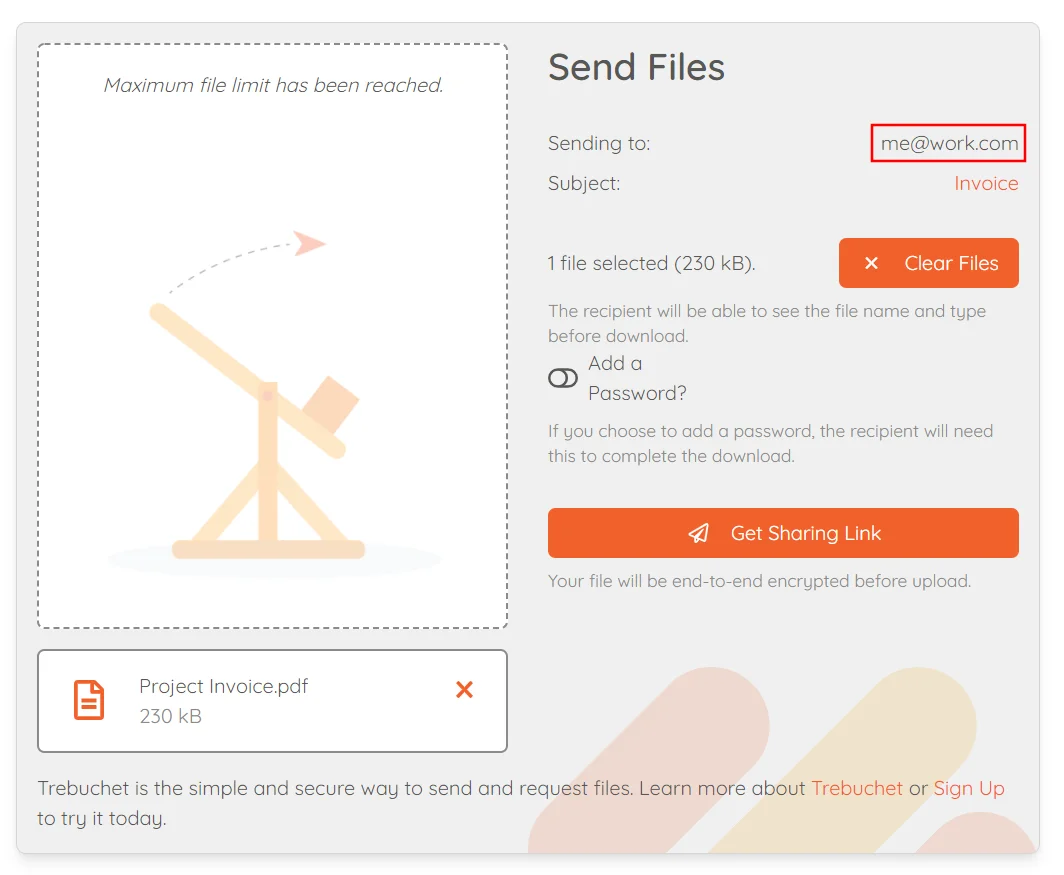
Easily and securely sending files to people with your Trebuchet account is great, but only allows you to push files to people. We wanted something that works in both directions for the paid tiers, so Trebuchet also supports requesting files from people.
If you’re signed in, you can create a share request to send to someone who has something you need. They can follow that link, and share files that are immediately encrypted and sent back to you. It’s clear from the interface that it’s a request from your account, and the files are going to you:
First Launch of Trebuchet
The free version is available now. It does have limits on monthly usage, but does not compromise on security. The paid for (but still cheap) Premium version has more features, including secure messages, sharing requests, and unlimited usage. And there’s further options for teams and organisations.
Finally, we wanted to make it customizable, so people who want a branded version can have share.yourcompany.com, for example, instead of our main version. So we have our own version, which is consistent with our domain name and branding, and is linked to our corporate Single Sign-On (and has dark mode, because we’re really cool):
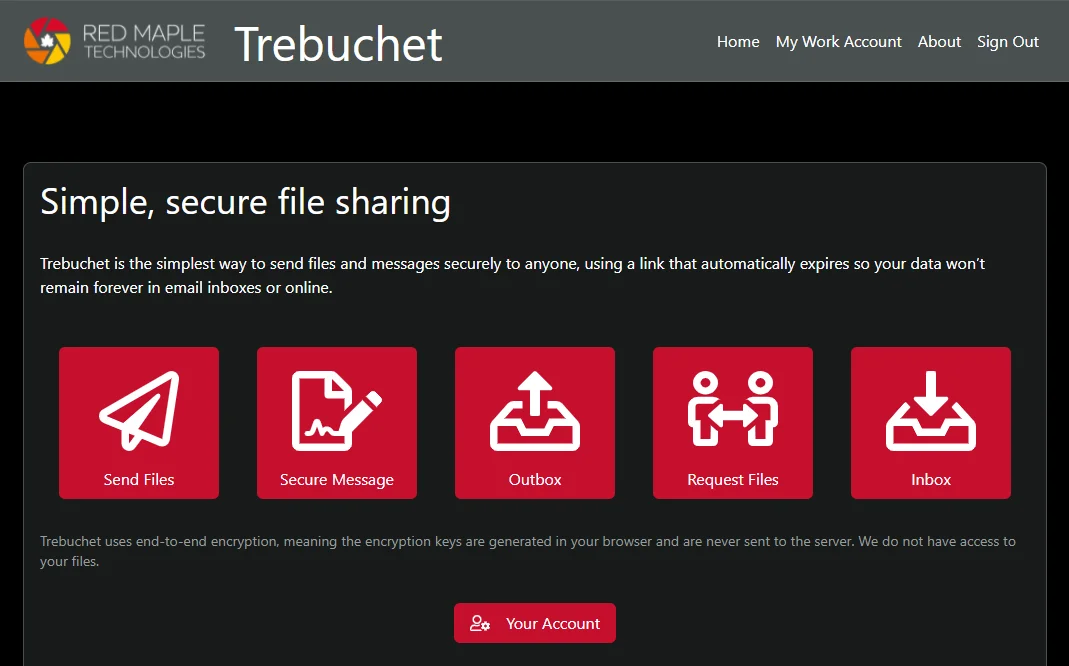
That’s soon going to be an option for everyone, under enterprise pricing.
Security
As a consultancy it’s always good to practice what you preach. As well as internal design and code reviews, we have had Trebuchet penetration tested by a third-party, and updated it in line with their recommendations. We plan to have it regularly tested, and will set up a coordinated vulnerability disclosure policy in the near future.
For more information on the technical gubbins, see the how it works page.
Future Plans
We’ve lots of plans for Trebuchet, most of which are aimed at making it better and easier to use for file sharing. For example, we’d like to make email integration easier, and looks at ways of making it easier to share between two Trebuchet users, and within teams. Regardless of the changes, security and privacy will always be paramount.
What’s in a name?
Clearly, the hardest part of building something is giving it a good name. Trebuchet was the internal name for the first version, and it stuck. We did eventually drop the explanation from the site, but it’s worth repeating if for no other reason than to explain the tenuous seige metaphor:
The Trebuchet has earned its place in history as indisputably the superior siege weapon of all time, with a structurally impressive counterweight and capability to launch a 90kg projectile over a distance of 300m. Whilst our cities are besieged far less frequently, the same cannot be said of your data.
Rich, when he built the first version
For those in need of brushing up on their ancient seige weaponry, have a read of the Wikipedia page. And if you’ve been inspired to build your own, here’s a nice instructional video






